We currently have a T3 line for about 28 people and it gets deadly slow during the day so I need something to help track down why. I'm assuming someone is downloading something that they may not be aware of.
Internet Traffic – Best Way to Monitor for Entire Office
internettraffic
Related Solutions
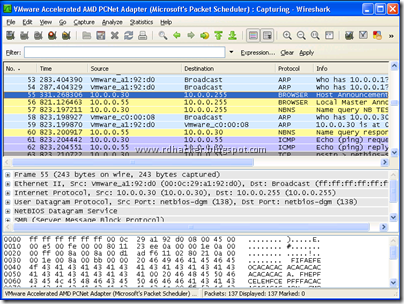
I'm sure there's a way to better interpret the info coming from your ISA server, but in case everything fails: "In wireshark we trust"
It runs on Windows too: http://www.wireshark.org/download.html
1.) Bandwidth != latency, and jitter matters. A dedicated leased line's latency is constant and is generally substantially lower than a DSL or FIOS connection. This can be a critical point for certain types of applications. The upstream bandwidth from a given POP is certainly a point of variability, but generally far less so than consumer-oriented concentrators which can suffer in non-intuitive ways under periods of congestion.
2.) Consistency of bandwidth - If you lease a DS-3 then you have that bandwidth available at all times and under all circumstances. Even business-grade DSL/cable/similar services are subject to variations in available bandwidth based on usage. There's more bandwidth available under most conditions, but potentially less under others.
3.) Availability - At least in the US, traditional leased lines can be had anywhere. If your facility happens to be in an industrial park or located somewhat remotely then cable/DSL/FIOS may simply not be available at all. This is especially true in many commercial settings where a SONET mux may already be present but other services aren't economically viable for SP's.
4.) Mixture of services - Many SP's will offer Internet transit bandwidth as well as private WAN service on the same physical pipe. While this can be accomplished on a shared medium, better results are often had on dedicated pipes. Also, as antiquated as it may sound there is still a lot of use of standard PRI's rather than SIP trunks for a lot of phone systems. These can be mapped into a timeslot along with other services.
5.) To your first point, ALL Internet service is multiplexed. That's kind of the point. Without oversubscription networks don't really make a lot of sense. Predictability of the behavior of oversubscription is the point - and this isn't something that has been a major design goal of transports dedicated to consumer transport.
In practice I'd generally rather see a straight Ethernet connection run natively or mapped over a SONET circuit for sites with substantial bandwidth requirements but there are plenty of instances where traditional SONET framing is really the only practical solution. For edge sites the consumer edge services (inclusive of so-called business grade) are generally both sufficient and attractively priced.
Best Answer
I would recommend against using wireshark to monitor traffic. You'll just get too much data, but you have a hard time analyzing the data. If you need to look at/troubleshoot the interaction between a couple machines, wireshark is great. As a monitoring tool, IMHO, wireshark is not quite the tool you need.
Profile the network traffic. Try out some actual monitoring tools: http://sectools.org/traffic-monitors.html. You're looking for Top Type of traffic (likely HTTP, but who knows), Top Talkers (should be your servers, but who knows), and potentially Malformed Traffic (large amount of TCP retransmissions, malformed packets, high rates of very small packets. Probably won't see, but who knows)
At the same time, work with your management to develop a network resource usage policy. In general, business terms, what business needs does the computer network exist to meet, and what are appropriate uses of the resource. This thing is costing money, so there has to be a business justification for its very existence. Your company has policies for handling the "petty cash" drawer, and I would bet your network infrastructure costs a lot more that. The key thing to focus on is not catching people doing bad things but rather watching for potential malicious activity that is degrading network functionality (i.e., the employees' ability to get their work done). Southern Fried Security Podcast and PaulDotCom Security Weekly cover information about creating appropriate security policies.
@John_Rabotnik idea for a proxy server was great. Implement a proxy server for web traffic. Compared to traditional firewalls, proxy servers give you much better visibility into what is going on as well as more granular control over what traffic to allow (for example, real web sites) and what traffic to block (URLs made up of [20 random characters].com)
Let people know - the network is having a problem. You are monitoring the network traffic. Give them a mechanism to register network slowdowns, and capture enough meta-data about the report so that in aggregate, you might be able to analyze network performance. Communicate with your coworkers. They want you to do a good job so that they can do a good job. You are on the same team.
As a general rule, block everything, and then allow what should be allowed. Your monitoring from step one should let you know what needs to be allowed, as filtered through your network usage/security policy. Your policy should also include a mechanism by which a manager can request new kinds of access be granted.
In summary, step one, the traffic monitoring (Nagios seems to be a standard tool) helps you figure out, in general, what is going on to stop the immediate pain. Steps 2 - 5 help prevent the problem in the future.